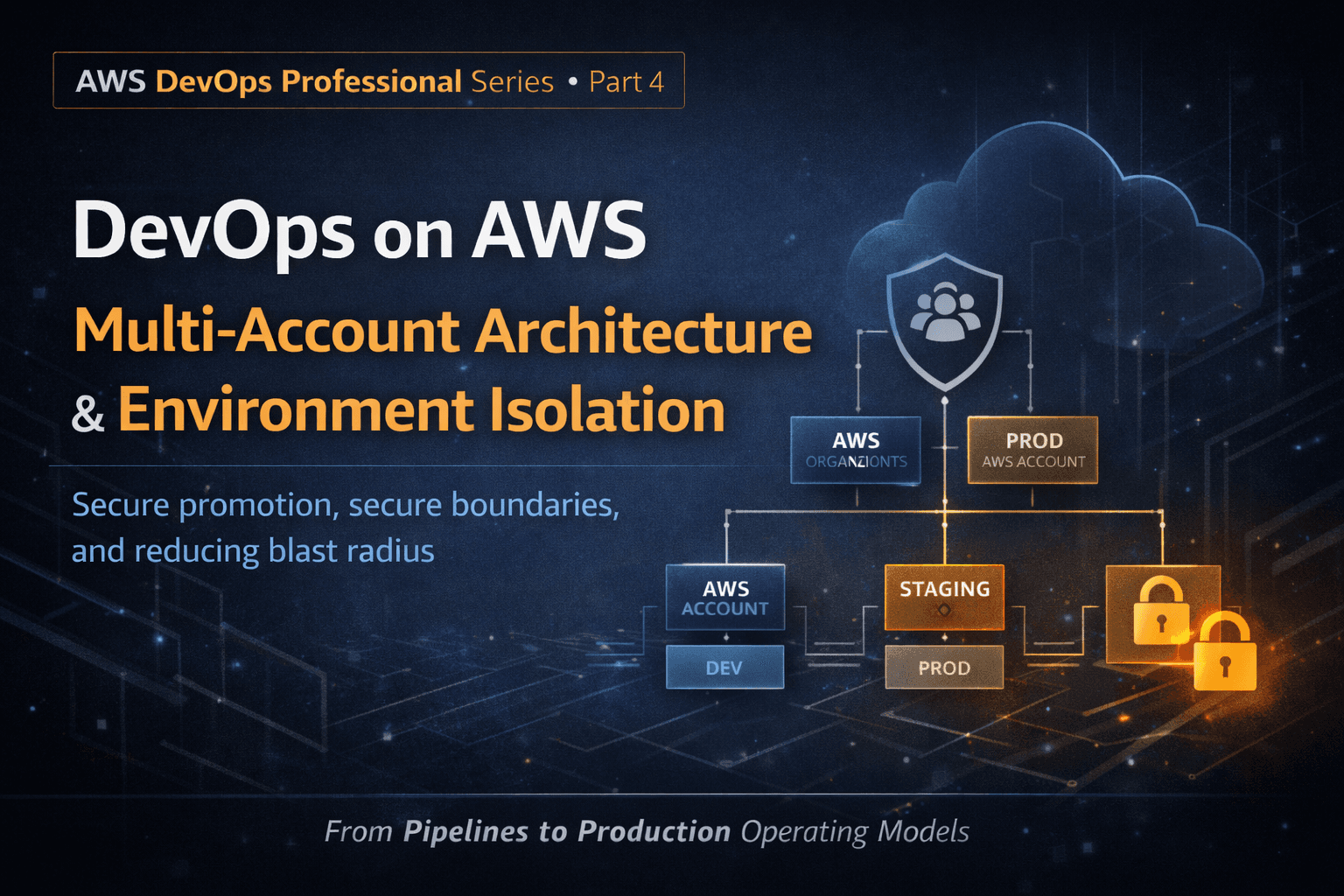
Part 4: Multi-Account Architecture, Environment Isolation, and Secure Promotion
At small scale, a single AWS account feels simple.
At scale, it becomes dangerous.
Most large-scale AWS failures are not caused by bad code :
they’re caused by poor isolation.
This post focuses on why multi-account architecture is foundational to AWS DevOps maturity, how environment isolation reduces blast radius, and how production systems safely promote change across accounts.
This is not an “AWS Organizations tutorial.”
This is about controlling risk at the account boundary.
Why Single-Account DevOps Fails at Scale
In early-stage systems, teams often run everything in one account:
Dev
Test
Staging
Production
Shared tooling
It works —> until it doesn’t.
Single-account systems eventually suffer from:
Accidental production changes
Over-permissive IAM roles
Shared failure domains
Unclear ownership boundaries
Inability to enforce different guardrails per environment
When everything lives together, blast radius is unlimited.
The AWS Account Is the Strongest Isolation Boundary
In AWS, an account provides:
Hard IAM separation
Service quota isolation
Billing visibility
Security boundary enforcement
Failure containment
This is why mature AWS DevOps systems treat accounts as environments, not just containers for resources.
Typical production-grade layouts:
One account per environment
(dev / test / staging / prod)One account per workload
Separate shared-services accounts
Separate security and logging accounts
Isolation is not overhead —> it’s protection.
AWS Organizations: Governance at Scale
AWS Organizations exists to solve a problem tooling cannot.
It enables:
Centralized account management
Hierarchical control using OUs
Policy enforcement before mistakes happen
Key mechanisms:
Service Control Policies (SCPs)
Consolidated billing
Account lifecycle automation
Important principle:
SCPs define what is impossible, not what is allowed
IAM grants permission.
SCPs remove dangerous possibilities.
This is critical for production safety.
Environment Isolation Is About Intentional Friction
High-risk environments should be harder to change.
Production should have:
Stronger access controls
Stricter approval paths
Tighter deployment conditions
Clear ownership
Development should have:
Faster iteration
Fewer guardrails
Lower blast radius
If prod is as easy to change as dev —> your system is fragile.
DevOps maturity includes adding friction in the right places.
CI/CD Across Multiple Accounts: The Right Way
Multi-account DevOps does not mean:
Manually copying artifacts
Re-running builds per environment
Duplicating pipelines everywhere
Production-grade pipelines follow one rule:
Build once. Promote many times.
Typical flow:
Build artifacts in a tooling account
Store immutable artifacts (ECR, S3, artifact repos)
Promote the same artifact through environments
Deploy using cross-account roles
This guarantees:
Consistency across environments
Traceability
Reliable rollback
Rebuilding per environment reintroduces risk.
Cross-Account Access: Trust, Not Convenience
Cross-account deployment relies on:
IAM roles with explicit trust policies
Least-privilege permissions
Clear separation of responsibilities
Pipelines should:
Assume roles into target accounts
Never share long-lived credentials
Be auditable
This is not just best practice —>
it’s how AWS expects production systems to operate.
Reducing Blast Radius at the Account Level
Account boundaries allow you to:
Contain bad deployments
Prevent lateral movement
Limit credential impact
Isolate compromised workloads
If a deployment fails in staging:
- Production remains untouched
If credentials leak:
- Damage is scoped
This is blast-radius control at the highest level.
Exam Insight: What AWS DevOps Professional Is Testing Here
The exam is not testing:
“Do you know what AWS Organizations is?”
It’s testing:
When to separate accounts vs environments
How to enforce governance without slowing teams
How to promote artifacts safely
How SCPs differ from IAM
How to limit blast radius beyond infrastructure
Correct answers often include:
Multi-account strategies
SCP-based guardrails
Centralized logging/security accounts
Cross-account CI/CD with role assumption
Think governance through architecture, not through process.
Production Reality Check
Multi-account systems:
Add complexity
Require planning
Demand discipline
But they pay for themselves the first time:
A bad deploy is contained
A permission mistake is blocked
A security incident is isolated
Single-account DevOps optimizes for speed.
Multi-account DevOps optimizes for survivability.
What’s Next (Part 5)
In Part 5, we’ll dive into:
Observability, Incident Response, and Learning from Failure
Metrics that actually matter
Designing actionable alerts
Reducing MTTR, not alert count
Incident response as a system
Turning outages into architectural improvements
Final Thought
DevOps is not just about deploying code.
It’s about designing systems where mistakes are inevitable - but disasters are optional.
Multi-account architecture is how AWS DevOps turns risk into something manageable.