🏗️ Part 4: Advanced Kubernetes Networking — Services, Ingress, and Traffic Flow
In Part 3, we explored the big picture of Kubernetes architecture — how the Control Plane, Worker Nodes, and components like Pods, Deployments, and StatefulSets work together to create resilient, scalable, and self-healing clusters.
Now, it’s time to zoom in on Kubernetes networking — how traffic flows inside the cluster and how users reach your applications from the outside.
🌐 Kubernetes Networking Overview
Kubernetes networking can be thought of in three layers:
Pod-to-Pod communication: Every Pod gets a unique IP and can talk to any other Pod in the cluster.
Pod-to-Service communication: Services abstract Pods behind stable endpoints.
External traffic: Ingress and LoadBalancers manage traffic from outside the cluster to your applications.
🧠 1️⃣ Core Networking Components
a) Kube-Proxy
Runs on every Worker Node.
Maintains iptables/IPVS rules for routing Service traffic to the correct Pods.
Provides internal load balancing across Pod replicas.
b) Services
Kubernetes Services provide stable endpoints to access Pods:
| Service Type | Purpose |
| ClusterIP | Internal-only communication between Pods (default) |
| NodePort | Exposes service on a static port on each Node |
| LoadBalancer | Integrates with cloud LBs (AWS ELB, Azure LB) for external access |
| ExternalName | Maps a Service to an external DNS name |
c) Ingress & Ingress Controllers
Manage HTTP/HTTPS traffic into the cluster.
Handle TLS termination, path-based routing, and host-based routing.
Examples: NGINX Ingress Controller, Traefik, HAProxy Ingress.
Example Ingress YAML:
apiVersion: networking.k8s.io/v1
kind: Ingress
metadata:
name: frontend-ingress
spec:
rules:
- host: frontend.example.com
http:
paths:
- path: /
pathType: Prefix
backend:
service:
name: frontend-svc
port:
number: 80
🛡️ 2️⃣ Network Policies
Control which Pods can communicate with each other.
Helps implement security segmentation inside the cluster.
Example YAML:
apiVersion: networking.k8s.io/v1
kind: NetworkPolicy
metadata:
name: db-access
spec:
podSelector:
matchLabels:
app: database
ingress:
- from:
- podSelector:
matchLabels:
app: api
🔗 3️⃣ How Traffic Flows
Internal Traffic:
Pod → ClusterIP Service → Kube-Proxy → Target Pod
External Traffic:
User → LoadBalancer / NodePort → Ingress Controller → Service → Pod
Kube-Proxy ensures traffic is routed to healthy Pods.
Ingress manages complex HTTP routing and TLS termination.
NetworkPolicies enforce security and isolation.
⚡ 4️⃣ Observability & Monitoring
To manage networking at scale, we need visibility:
Prometheus: Metrics for Pod traffic, Service response times, and network latency.
Grafana: Visualize traffic flow and performance trends.
ELK / Fluentd: Collect and analyze network logs for debugging.
🧩 5️⃣ Real-World Scenario
Imagine an e-commerce app:
Frontend Pods use ClusterIP to talk to backend Pods.
Payment API is exposed via NodePort.
Ingress routes
www.shop.comto frontend Pods and/apito backend Pods.NetworkPolicies restrict database Pods to accept traffic only from backend Pods.
This ensures scalable, secure, and observable traffic flow.
🧭 What’s Next
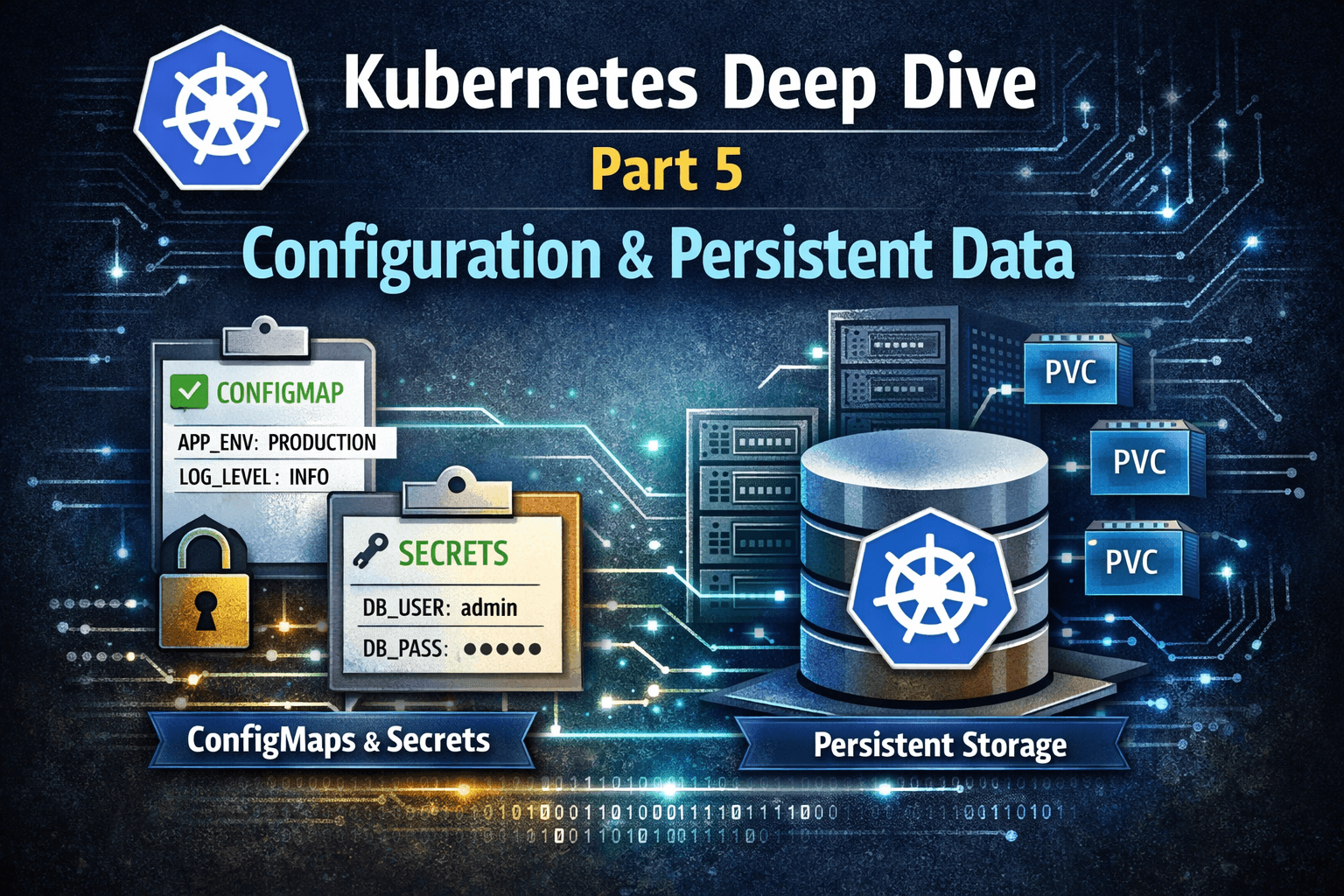
Now that we understand Kubernetes networking, the next step is stateful workloads — ConfigMaps, Secrets, Persistent Volumes, and StatefulSets.
In Part 5, we’ll see how Kubernetes manages application configuration and persistent data, making it ready for enterprise-grade workloads.